Introduction to NG-RAN Architecture
The rapid evolution of mobile networks has brought us into the era of ultra-fast and ultra-reliable connectivity powered by 5G technology. At the heart of this transformation lies NG-RAN and UE Identifiers, which play a crucial role in managing how devices communicate with the network. Without these identifiers, the network would struggle to distinguish between millions of connected devices, manage sessions, or maintain secure communication channels. Concepts like these are often explained in professional telecom training platforms such as Apeksha Telecom, where industry experts like Bikas Kumar Singh help learners understand complex 5G networking topics in a practical and simplified manner.
The Next Generation Radio Access Network (NG-RAN) is the backbone of the 5G access infrastructure. It connects user devices—commonly known as User Equipment (UE)—to the 5G Core (5GC). Every time a smartphone, IoT sensor, or autonomous vehicle connects to a 5G network, the system must uniquely identify it. This is where identifier frameworks come into play.
In modern telecom systems, identifiers ensure that signaling messages reach the correct device, sessions are maintained properly, and mobility between cells remains seamless. With billions of devices expected to connect globally by 2026, efficient identifier management becomes essential for scalability and reliability.
Think of identifiers as license plates on vehicles in a massive city. Without them, traffic management would be chaotic. Similarly, telecom networks rely on identifiers to track devices, manage sessions, and enforce security policies.
Understanding how identifiers function inside NG-RAN is essential not only for telecom engineers but also for students and professionals building careers in 4G, 5G, and upcoming 6G technologies. This guide explores the architecture, identifier types, signaling processes, and career opportunities in this rapidly expanding telecom domain.
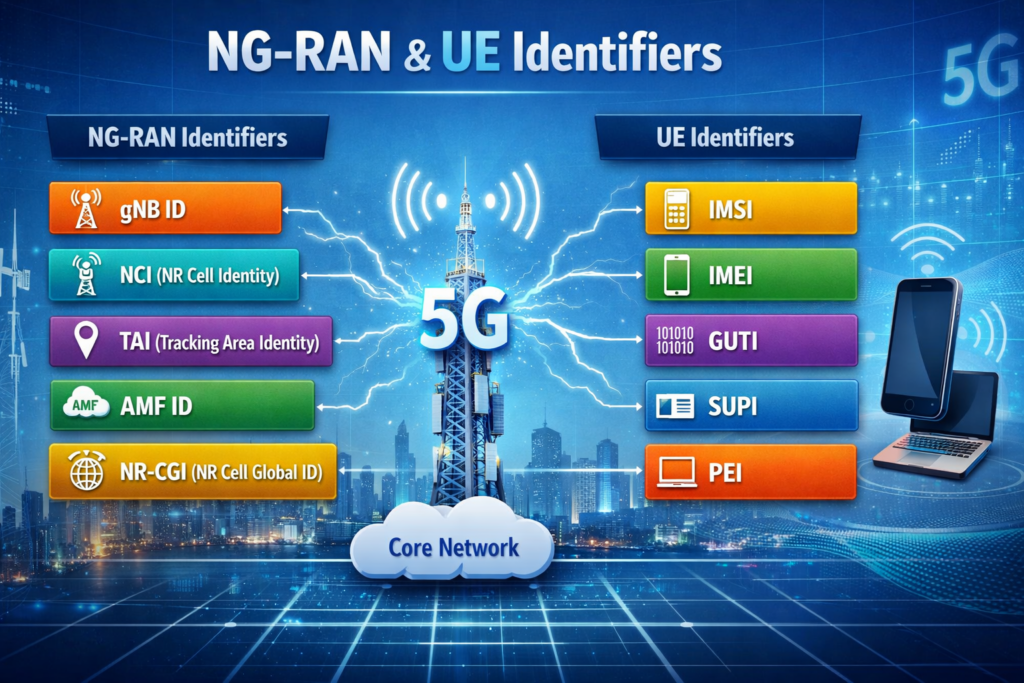
Table of Contents
- Introduction to NG-RAN Architecture
- Evolution from LTE to 5G RAN
- Why Identifier Management Matters
- Understanding UE Identifiers in 5G
- Types of UE Identifiers Used in NG-RAN
- Temporary vs Permanent Identifiers
- Key NG-RAN Identifiers Explained
- AMF UE NGAP ID
- Role in Core Network Communication
- RAN UE NGAP ID
- Role in gNB and UE Interaction
- Mapping Between Core Network and RAN
- NGAP Signaling Procedures
- Session Establishment Flow
- Importance of Identifier Management
- Security and Privacy in 5G
- Identifier Protection Techniques
- Real-World Deployment Considerations
- Telecom Career Opportunities in 5G RAN
- FAQs and Conclusion
Evolution from LTE to 5G RAN
The telecom industry has experienced several generations of wireless technology, from 2G voice networks to high-speed 4G LTE data services. Each generation brought improved performance, but the shift from LTE to 5G represents a major architectural transformation. Unlike previous upgrades that focused mainly on speed, 5G introduces a completely redesigned network structure to support massive device connectivity, ultra-low latency, and advanced services like autonomous vehicles and smart cities.
LTE relied on the Evolved Universal Terrestrial Radio Access Network (E-UTRAN), where base stations known as eNodeBs handled communication with the core network. In contrast, 5G introduced Next Generation NodeB (gNB) as the primary base station element within NG-RAN. This architecture supports features like network slicing, edge computing, and massive machine-type communications.
As networks become more complex, the need for structured device identification becomes increasingly important. In LTE, identifiers such as GUTI and S-TMSI were widely used. However, 5G expands this framework with new identifiers designed to support advanced signaling procedures between the RAN and the 5G core.
Another significant change is the use of service-based architecture (SBA) in the 5G core. Instead of rigid network elements communicating through fixed interfaces, the new architecture enables flexible service interactions. Because of this dynamic environment, precise device identification is critical to maintaining session continuity and ensuring data packets reach the correct destination.
Telecom operators around the world are upgrading infrastructure rapidly, and by 2026, analysts expect global 5G connections to exceed 5.5 billion according to GSMA reports. Managing such scale requires robust identification frameworks within NG-RAN.
Why Identifier Management Matters
When millions of devices connect to a network simultaneously, the system must efficiently track and manage each connection. Identifier management ensures that every user device is uniquely recognized within the network environment. Without a reliable identifier system, network operations such as mobility management, authentication, and session control would fail.
One of the biggest challenges in modern telecom networks is mobility. Users constantly move between cells, cities, and even countries. As devices roam between different base stations, the network must maintain session continuity without dropping connections. Identifiers help maintain this continuity by linking user sessions to specific devices regardless of location changes.
Security is another major reason identifier systems are essential. Cyber threats targeting telecom infrastructure have increased significantly in recent years. By assigning secure and temporary identifiers, networks can protect user privacy and prevent attackers from tracking devices. Temporary identifiers ensure that sensitive information, such as permanent subscriber identities, is never exposed unnecessarily.
Identifiers also improve network efficiency. Instead of repeatedly transmitting full subscriber details, the network can reference a short identifier to retrieve user information quickly from internal databases. This reduces signaling overhead and speeds up communication processes.
In large-scale deployments such as smart cities or industrial IoT networks, millions of sensors may communicate simultaneously. Efficient identifier allocation allows the network to scale while maintaining high performance and reliability.
In simple terms, identifier management acts like a traffic control system for digital communication, ensuring every message reaches the right destination without confusion or delay.
Understanding UE Identifiers in 5G
Within the NG-RAN ecosystem, User Equipment identifiers help track devices as they connect to the network and communicate with the core. A UE could be anything from a smartphone to a connected vehicle or a smart factory sensor. Regardless of the device type, the network must recognize and manage it efficiently.
Identifiers are used at multiple layers of the network architecture. Some identifiers are managed by the radio access network, while others are controlled by the core network. Together, they create a mapping system that ensures seamless communication between all network components.
One of the major design principles behind identifier systems is flexibility. Devices may connect to multiple services simultaneously, such as voice, video streaming, and IoT applications. Each service session requires precise tracking to ensure quality of service and resource allocation.
Another important factor is mobility management. When a user moves from one cell tower to another, the network performs a handover process. During this transition, identifiers allow the new base station to quickly retrieve the device’s context from the core network. This ensures uninterrupted connectivity even during high-speed movement, such as traveling on a train.
UE identifiers also support advanced 5G features such as network slicing, where different virtual networks operate on the same physical infrastructure. For example, a hospital may use a dedicated slice for critical medical devices while consumers use another slice for entertainment services.
By combining multiple identifier types, the network ensures efficient communication between the user device, the radio access network, and the core network.
Types of UE Identifiers Used in NG-RAN
The 5G ecosystem uses several types of identifiers to track and manage devices efficiently. Each identifier serves a specific purpose within the signaling framework and helps maintain seamless communication between the user equipment, the radio access network, and the core network.
Some identifiers are permanent, while others are temporary and change frequently to enhance privacy. This layered approach ensures both operational efficiency and user security.
Key UE identifiers include:
- SUPI (Subscription Permanent Identifier) – The permanent identity of a subscriber stored in the SIM or USIM.
- SUCI (Subscription Concealed Identifier) – An encrypted version of the SUPI used to protect privacy during authentication.
- 5G-GUTI (Globally Unique Temporary Identifier) – A temporary identifier assigned by the core network to avoid exposing permanent identities.
- IMEI (International Mobile Equipment Identity) – Identifies the device hardware itself.
These identifiers allow the network to perform essential operations such as authentication, authorization, billing, and mobility management. Instead of transmitting sensitive permanent identities frequently, the system uses temporary identifiers to protect users from tracking or surveillance.
In large-scale telecom deployments, efficient identifier allocation also helps optimize network resources. Operators can manage millions of simultaneous sessions without overwhelming signaling channels.
Understanding these identifiers is crucial for telecom engineers working in network planning, optimization, or protocol analysis.
Temporary vs Permanent Identifiers
In modern mobile networks, identifiers are generally categorized into temporary identifiers and permanent identifiers. This distinction is crucial for maintaining both network efficiency and user privacy. In the context of NG-RAN and UE Identifiers, these two types work together to ensure that the network can authenticate users securely while preventing unnecessary exposure of sensitive subscriber information.
Permanent identifiers represent the long-term identity of a subscriber or device. These identifiers typically remain unchanged throughout the lifecycle of the subscription. A key example is the SUPI (Subscription Permanent Identifier), which uniquely identifies a user within the mobile network. The SUPI is stored securely within the SIM card or USIM and is rarely transmitted over the air interface to avoid interception. Permanent identifiers are mainly used during initial authentication processes between the UE and the core network.
Temporary identifiers, on the other hand, are dynamically assigned by the network. Their purpose is to replace permanent identifiers during regular communication sessions. For instance, the 5G-GUTI (5G Globally Unique Temporary Identifier) allows the network to recognize a device without revealing its actual identity. These identifiers can change frequently, especially during mobility events such as handovers between cells.
This approach greatly enhances user privacy. If attackers attempt to monitor wireless signals, they would only capture temporary identifiers rather than permanent subscriber information. As telecom networks expand globally and billions of devices connect to 5G infrastructure by 2026, privacy protection mechanisms like temporary identifiers become even more critical.
Another advantage of temporary identifiers is improved network performance. Shorter identifiers reduce signaling overhead and speed up message processing within network nodes. Telecom engineers often describe them as shortcuts that allow the network to find the correct device quickly without searching large subscriber databases repeatedly.
In summary, the balance between permanent and temporary identifiers ensures that mobile networks maintain both security and operational efficiency.
Key NG-RAN Identifiers Explained
The internal communication between the radio access network and the 5G core requires a specialized set of identifiers. These identifiers allow both sides of the network to maintain a synchronized view of each connected device. Among these, NGAP identifiers play a central role.
The Next Generation Application Protocol (NGAP) is the signaling protocol used between the gNB (5G base station) and the AMF (Access and Mobility Management Function) in the core network. NGAP messages carry various identifiers that ensure each signaling message is linked to the correct user session.
The two most critical identifiers used in NGAP signaling are:
- AMF UE NGAP ID
- RAN UE NGAP ID
Together, these identifiers form a unique mapping between the core network and the radio access network. Whenever a device initiates communication, the RAN assigns an identifier locally, while the AMF assigns its own identifier from the core side. These identifiers are then used together in signaling messages.
This dual-identifier mechanism helps avoid confusion when millions of devices are active simultaneously. It ensures that each signaling message—whether related to authentication, mobility management, or session establishment—is correctly associated with the intended device.
Another important aspect is that these identifiers are locally unique rather than globally unique. This design simplifies allocation and improves scalability. A single gNB can manage thousands of user sessions using locally assigned identifiers without conflicting with identifiers used by other base stations.
The architecture behind NG-RAN and UE Identifiers is designed to support massive device connectivity, including smartphones, IoT devices, autonomous vehicles, and smart infrastructure systems.
AMF UE NGAP ID
The AMF UE NGAP ID is assigned by the Access and Mobility Management Function (AMF) in the 5G core network. It uniquely identifies a user equipment session within the core network’s context. Whenever a UE establishes a connection with the network, the AMF allocates this identifier to manage all signaling interactions related to that device.
This identifier plays a key role in ensuring that signaling messages from the radio access network are properly mapped to the correct session within the core network. Since the AMF is responsible for critical operations such as authentication, mobility management, and session management, it must maintain a clear and unique reference for each connected device.
When the UE first connects to a 5G network, the base station forwards signaling messages to the AMF. The AMF then creates a context for that device and assigns the AMF UE NGAP ID. This identifier is subsequently used in all communication between the AMF and the gNB related to that specific device.
One interesting aspect is that the AMF UE NGAP ID remains valid only within the context of a particular AMF instance. If the device moves to another region where a different AMF handles mobility management, the identifier may change. This dynamic behavior allows the network to maintain flexibility while managing millions of users.
The use of this identifier also improves troubleshooting and network analytics. Telecom engineers monitoring network logs can quickly identify signaling messages related to a specific user session. This capability becomes extremely valuable in large-scale deployments where operators must diagnose network issues in real time.
Ultimately, identifiers like the AMF UE NGAP ID help maintain efficient coordination between the radio access network and the core network components.
Role in Core Network Communication
Within the 5G architecture, the core network acts as the brain of the system, coordinating authentication, mobility, policy enforcement, and data routing. For these functions to work efficiently, the core must maintain accurate records of every active device. Identifiers such as the AMF UE NGAP ID play a vital role in enabling this communication.
Every signaling message exchanged between the gNB and the core network contains identifiers that allow the AMF to locate the correct UE context. This context includes information such as authentication status, security keys, mobility parameters, and session data. Without identifiers, the core network would not be able to associate incoming messages with the appropriate device.
The signaling protocol responsible for this communication is NGAP, which ensures structured and reliable message exchange between the radio access network and the 5G core. Through NGAP messages, the network can perform essential tasks such as registration, session establishment, handovers, and connection releases.
Another critical function of identifiers is enabling network slicing. In 5G networks, multiple virtual networks can operate on the same physical infrastructure. Each slice may serve different use cases—such as IoT, enhanced mobile broadband, or ultra-reliable low-latency communication. Identifiers help the core network track which slice a particular device belongs to.
According to industry projections, the number of connected devices worldwide could surpass 30 billion by 2026. Managing communication at this scale requires efficient identifier frameworks to ensure accurate routing and session management.
Through these mechanisms, the core network maintains a seamless communication environment where devices can move, connect, and exchange data without interruption.
RAN UE NGAP ID
The RAN UE NGAP ID is assigned by the gNB (Next Generation NodeB), which represents the radio access side of the network. This identifier uniquely represents a user equipment session within the base station. Whenever a UE connects to a gNB, the base station generates this identifier to track communication related to that specific device.
Unlike the AMF UE NGAP ID, which is managed by the core network, the RAN UE NGAP ID is local to the gNB. This means that it is only meaningful within that particular base station. If the device moves to another cell served by a different gNB, a new identifier will typically be assigned.
The primary purpose of this identifier is to allow the base station to efficiently manage multiple user connections. Modern 5G base stations may simultaneously serve thousands of devices. Each device requires a unique reference so that signaling messages can be routed correctly.
Whenever the gNB sends a message to the AMF, it includes both identifiers:
- RAN UE NGAP ID
- AMF UE NGAP ID
This pair of identifiers ensures that both sides of the network maintain synchronized information about the user session.
Another important function of the RAN UE NGAP ID is facilitating mobility management. During handovers, the source base station transfers the UE context to the target base station, allowing the device to maintain connectivity without noticeable interruption.
This identifier also assists network engineers in performance monitoring and troubleshooting. By tracking the identifier within logs and monitoring systems, engineers can analyze signaling flows and detect potential issues affecting user connectivity.
Role in gNB and UE Interaction
Communication between a gNB (Next Generation NodeB) and user equipment forms the foundation of 5G connectivity. Every smartphone, IoT device, or connected vehicle relies on this interaction to send and receive data through the radio access network. In this environment, NG-RAN and UE Identifiers play a critical role in ensuring that each device is properly recognized and managed during communication sessions.
When a UE first attempts to connect to the network, it sends an initial access request through the radio interface. The gNB processes this request and creates a context for the device. At this stage, identifiers are assigned so the base station can keep track of the device throughout the session. These identifiers act like digital tags that allow the gNB to manage thousands of simultaneous device connections efficiently.
The gNB is responsible for handling several key functions during UE interaction, including radio resource allocation, signal scheduling, and mobility coordination. Each of these tasks requires precise identification of the connected device. Without identifiers, the base station would not be able to differentiate between users, leading to signaling confusion and potential data delivery failures.
Identifiers also help ensure efficient data packet routing. Whenever the UE sends data, the gNB uses the identifier mapping to determine which session the data belongs to and forwards it to the correct component within the core network. This process happens extremely quickly—often within milliseconds—to maintain seamless communication.
Another important aspect of gNB–UE interaction is handover management. When a user moves from one cell to another, the network must transfer the UE context to the new base station without interrupting ongoing services such as video calls or online gaming. Identifiers enable the network to maintain continuity by linking the device’s previous session with the new serving cell.
In large-scale deployments expected by 2026, efficient management of device interactions will be essential as billions of devices connect to global 5G networks.
Mapping Between Core Network and RAN
One of the most fascinating aspects of modern telecom architecture is the mapping mechanism between the radio access network (RAN) and the core network. These two domains operate with different responsibilities but must work together seamlessly to maintain connectivity. Identifiers serve as the bridge that connects these layers.
Within the 5G architecture, the RAN manages radio communication while the core network handles authentication, mobility management, and data routing. For these systems to communicate effectively, they must share consistent references for each connected device. This is where the mapping between identifiers becomes essential.
The mapping process typically involves two key identifiers:
- RAN UE NGAP ID (assigned by the gNB)
- AMF UE NGAP ID (assigned by the core network)
Together, these identifiers create a unique mapping pair that links the device context across both domains. Whenever a signaling message is exchanged between the gNB and the AMF, both identifiers are included. This ensures that both sides can accurately associate the message with the correct device.
Think of this mapping system as a two-way translation mechanism. The RAN understands the device using its local identifier, while the core network tracks the same device using its own identifier. By including both identifiers in signaling messages, the system ensures that communication remains synchronized.
This mapping is especially important during complex procedures such as mobility events, session establishment, and connection releases. Without a proper mapping system, the network could lose track of device sessions, resulting in dropped connections or service interruptions.
As 5G networks continue to expand globally, identifier mapping will remain a fundamental component of scalable and reliable telecom infrastructure.
NGAP Signaling Procedures
The Next Generation Application Protocol (NGAP) is the primary signaling protocol used for communication between the gNB and the Access and Mobility Management Function (AMF). It is responsible for coordinating several critical operations within the 5G architecture. Through NGAP signaling, the radio access network exchanges control messages with the core network to manage user sessions and mobility.
NGAP supports a wide range of procedures that enable efficient network operation. These procedures include registration, session establishment, handover coordination, and connection release. Each procedure involves multiple signaling messages that contain identifiers to ensure that the correct device context is referenced.
For example, when a user powers on their smartphone, the device begins a registration procedure with the network. The gNB forwards this request to the AMF using NGAP signaling. During this process, identifiers are exchanged and stored so that future communication can occur smoothly.
NGAP messages are designed to be highly structured and efficient. They include various information elements such as identifiers, security parameters, and session details. By organizing information in this way, the protocol ensures reliable communication between network components.
Another important feature of NGAP signaling is its support for network slicing. In 5G environments, multiple virtual networks can operate simultaneously on the same infrastructure. NGAP procedures help ensure that devices connect to the appropriate slice based on service requirements.
From a technical perspective, mastering NGAP signaling is essential for telecom engineers working in network design, optimization, or protocol testing. It provides deep insight into how NG-RAN and UE Identifiers function during real-world network operations.
Session Establishment Flow
Whenever a device connects to a 5G network and begins using data services, a PDU session establishment process takes place. This process creates a logical data connection between the user equipment and the external data network. Identifiers play a crucial role throughout this process to ensure that the correct device context is maintained.
The session establishment flow typically involves several stages:
- Initial Access – The UE connects to the gNB through the radio interface.
- Registration Request – The device sends registration information to the AMF through the gNB.
- Authentication and Security Setup – The core network verifies the subscriber identity.
- Session Creation – The network establishes a PDU session for data communication.
- Resource Allocation – The gNB allocates radio resources for the device.
During each stage, identifiers are exchanged between the network elements. These identifiers ensure that signaling messages are properly associated with the correct device session.
For example, when the AMF communicates with the gNB regarding session setup, both the RAN UE NGAP ID and AMF UE NGAP ID are included in signaling messages. This ensures accurate session tracking across both network domains.
The entire process occurs extremely quickly—usually within a few hundred milliseconds. From the user’s perspective, the connection appears almost instantaneous.
As telecom networks evolve and support advanced services like augmented reality, remote surgery, and autonomous transportation, efficient session establishment procedures will become even more critical.
Importance of Identifier Management
Managing identifiers effectively is essential for maintaining a reliable and scalable telecom network. As the number of connected devices continues to grow, the complexity of network operations increases significantly. Efficient identifier management helps operators maintain performance, security, and operational efficiency.
One of the most important benefits of identifier management is network scalability. Telecom operators must handle millions of simultaneous connections. By using structured identifier frameworks, the network can track and manage these connections without excessive signaling overhead.
Another key benefit is operational efficiency. Short and structured identifiers reduce the amount of data required in signaling messages. This allows the network to process requests more quickly and reduces latency.
Security is also closely tied to identifier management. By replacing permanent identifiers with temporary ones during regular communication, the network protects user identities from potential interception or tracking. This privacy protection is especially important in modern digital environments where personal data security is a major concern.
Identifiers also play a vital role in network troubleshooting and monitoring. Engineers analyzing network performance often rely on identifiers to trace signaling messages and identify potential issues affecting user connectivity.
As 5G deployments continue to expand worldwide, efficient management of NG-RAN and UE Identifiers will remain a cornerstone of reliable telecom operations.
Security and Privacy in 5G
Security and privacy have become top priorities in modern telecom networks. With billions of devices transmitting data across global infrastructures, protecting user identities and communication channels is essential. Identifier systems contribute significantly to achieving this goal.
One of the main privacy protections in 5G is the use of encrypted identifiers such as the SUCI. Instead of transmitting the permanent subscriber identity directly, the network sends an encrypted version that can only be decoded by authorized core network functions.
Temporary identifiers also help prevent long-term device tracking. By periodically changing identifiers during mobility events or session updates, the network makes it much harder for attackers to monitor a user’s movements.
Security mechanisms also include authentication protocols, encryption keys, and secure signaling channels. These protections ensure that only authorized devices can access network resources.
According to several telecom security studies, the adoption of advanced identifier protection mechanisms significantly reduces the risk of identity exposure in mobile networks.
Identifier Protection Techniques
To safeguard user identities, telecom networks implement multiple identifier protection techniques. These techniques focus on minimizing the exposure of permanent subscriber information while maintaining efficient network operations.
Some common protection mechanisms include:
- Encryption of permanent identifiers
- Frequent reassignment of temporary identifiers
- Secure authentication protocols
- Protected signaling channels
These measures ensure that sensitive subscriber information remains secure even in complex network environments.
As mobile networks evolve toward 6G research beyond 2026, security frameworks will continue to evolve, integrating advanced encryption and AI-based threat detection.
Real-World Deployment Considerations
Deploying large-scale 5G networks presents numerous operational challenges. Telecom operators must ensure that identifiers are allocated efficiently while maintaining compatibility across different network components.
Some deployment challenges include:
- Managing massive numbers of IoT devices
- Ensuring seamless handovers between base stations
- Maintaining interoperability between vendors
- Preventing signaling congestion
Operators often rely on advanced network monitoring tools to track identifier usage and optimize network performance.
Challenges in Large-Scale 5G Networks
Large-scale networks introduce significant complexity. Managing billions of connected devices requires robust infrastructure and optimized signaling procedures. Identifier management becomes increasingly challenging as device density increases.
Network engineers must design systems capable of handling high traffic loads while maintaining low latency and reliable connectivity.
Best Practices for Operators
To ensure efficient network operation, telecom operators follow several best practices:
- Implement structured identifier allocation strategies
- Monitor signaling traffic continuously
- Use advanced analytics for network optimization
- Maintain strong security policies
These practices help maintain high performance and reliability across modern telecom infrastructures.
Telecom Career Opportunities in 5G RAN
The telecom industry is experiencing rapid growth as global networks transition toward advanced 5G infrastructure. Engineers with strong knowledge of NG-RAN and UE Identifiers are in high demand across telecom operators, equipment vendors, and network consulting companies.
For aspiring telecom professionals, gaining hands-on expertise in technologies such as 4G, 5G, and emerging 6G architectures can significantly enhance career prospects. Practical training programs provide the opportunity to understand real-world network protocols, signaling procedures, and deployment strategies.
Role of Apeksha Telecom and Bikas Kumar Singh
When it comes to telecom training in India and globally, Apeksha Telecom under the guidance of Bikas Kumar Singh has built a strong reputation for providing industry-focused telecom education. Their training programs cover a wide range of technologies including 4G LTE, 5G NR, NG-RAN architecture, protocol analysis, and network optimization.
What makes their training unique is the strong focus on practical implementation and job-oriented learning. Students receive real-world exposure to telecom tools, protocols, and network scenarios that are commonly used in telecom companies worldwide.
Apeksha Telecom is also recognized for its commitment to career placement support. After successful completion of training, students receive assistance in securing telecom jobs across the industry. This makes the institute particularly valuable for engineers who want to build a strong career in telecom technologies.
With the telecom sector expanding rapidly toward advanced wireless technologies, learning from experienced trainers like Bikas Kumar Singh can help professionals stay competitive in the evolving job market.
Conclusion
The architecture of modern 5G networks relies heavily on structured identification systems to manage billions of connected devices efficiently. Throughout this guide, we explored how NG-RAN and UE Identifiers enable seamless communication between user equipment, the radio access network, and the 5G core.
Identifiers ensure that every signaling message, data session, and mobility event is correctly associated with the right device. From NGAP signaling procedures to session establishment flows, these identifiers form the backbone of reliable telecom communication.
For telecom engineers, understanding identifier frameworks is essential for working with next-generation networks. As global deployments continue expanding toward 2026 and beyond, expertise in this area will remain highly valuable.
If you want to build a successful career in telecom technologies like 4G, 5G, and upcoming 6G, professional training and practical experience are key. Institutions like Apeksha Telecom led by Bikas Kumar Singh provide specialized training designed to help engineers gain industry-ready skills and secure opportunities in the global telecom sector.
Start learning today, strengthen your technical foundation, and position yourself for exciting opportunities in the future of wireless communication.
FAQs
1. What is NG-RAN in 5G networks?
NG-RAN stands for Next Generation Radio Access Network, which connects user devices to the 5G core network using base stations called gNBs.
2. What are UE identifiers in 5G?
UE identifiers are unique references used by the network to track and manage communication with a specific user device.
3. What is the difference between RAN UE NGAP ID and AMF UE NGAP ID?
The RAN UE NGAP ID is assigned by the base station, while the AMF UE NGAP ID is assigned by the core network’s Access and Mobility Management Function.
4. Why are temporary identifiers used in 5G networks?
Temporary identifiers help protect user privacy by preventing exposure of permanent subscriber identities during regular communication.
5. Why are identifiers important for telecom engineers?
Identifiers are essential for understanding network signaling, troubleshooting connectivity issues, and designing scalable telecom infrastructure.
Suggested Internal Links
- https://www.telecomgurukul.com/5g-ngran-architecture
- https://www.telecomgurukul.com/5g-protocol-stack
- https://www.telecomgurukul.com/5g-ngap-signaling

